Breaking Pedersen Hashes in Practice | NCC Group Research Blog | Making the world safer and more secure

Veracode RPA+BI DetailedReport A2019 6 Mar 2021 Patch Build 8122 | PDF | Penetration Test | Java (Programming Language)
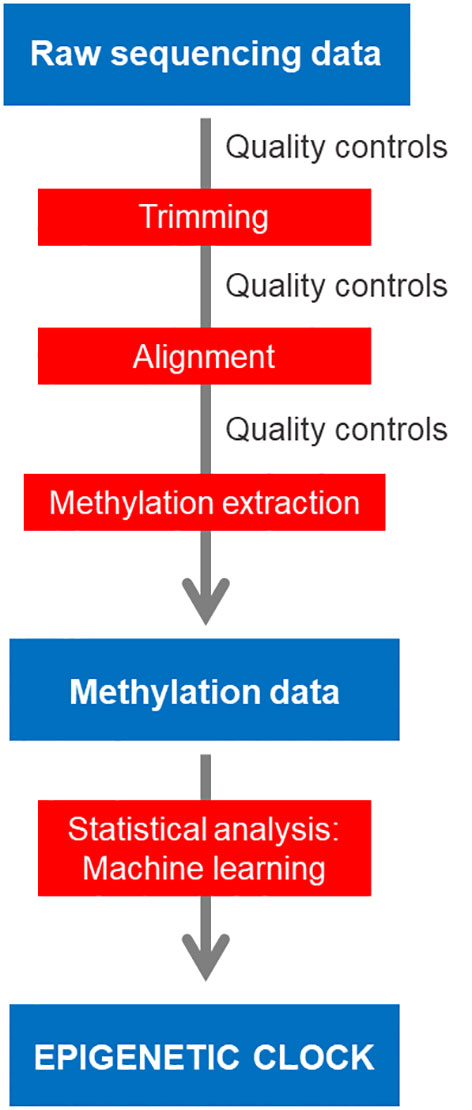
Frontiers | Bioinformatic analysis for age prediction using epigenetic clocks: Application to fisheries management and conservation biology

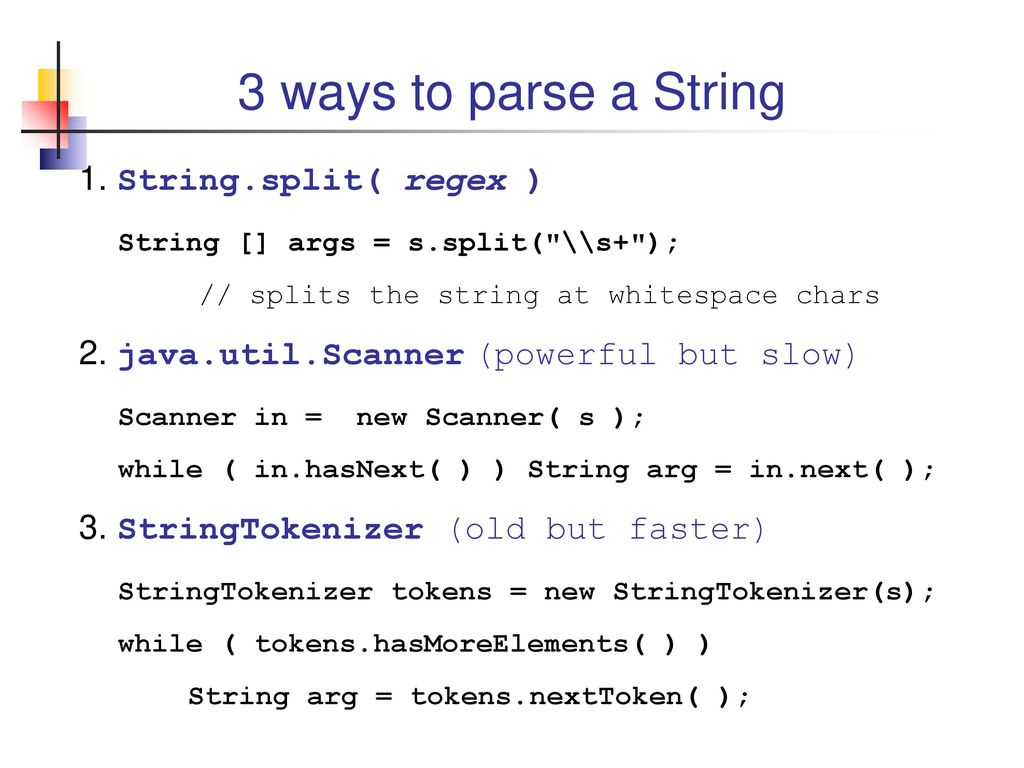
Javarevisited: String replaceAll() example - How to replace all characters and substring from String